VeryPDF Cloud PDF DRM Protector
https://www.verypdf.com/app/cloud-pdf-drm-security/index.html
Methods To Copy Protect PDF
There are vast differences between software that perform the same functions, and although encryption is generally used to preserve the integrity of those functions, in some cases the encryption may not be adequate and in others it may not exist beyond masking the file's properties*:
Prevent changes to PDF document
Adobe Acrobat is a well know PDF editor/creator which provides options for locking a PDF to prevent changes to its contents. Some other PDF editors also provide this option which usually required the use of a password for an author to make any changes.
Prevent printing of PDF document
As above, printing of a PDF can be prevented by locking with a password. This may prevent a user from using print controls within a reader but may not prevent them from using other print commands. Proper print control needs to control all devices connected to a computer including printer drivers (plugins) such as those used to convert documents to PDF.
Password protect PDF document
Password protection is probably the most commonly employed method of restricting unauthorized access to a PDF documents contents. When a password is applied an user wishing to open that PDF needs to type in the correct password before the document will open. However anyone wanting to distribute your document only needs to include the password with it. As already mentioned, the security of passwords stored in PDF are only as good as the encryption used to hide them**.
Set expire date on PDF document
Another popular method of protecting PDF is by applying an expiry date after which the PDF cannot be opened. This is most useful for making information available for a limited time and limiting sharing to a set window of opportunity. For example an author can send a document to someone and after say 5 days that PDF will no longer be accessible... to anyone. Unfortunately most readers depend on local computer time, which is the time displayed on the user's computer, and such expiration can be thwarted by simply turning back the computer clock. VeryPDF Cloud PDF DRM Protector solves this problem by offering the choice of using online time server checks.
Control access to PDF document
Access control of a PDF is basically about limiting just who can open the document. Often referred to as digital rights management but more aptly known as "document rights management", DRM requires a means of assigning authority for an individual user to open the document. Early forms of DRM for documents used certificates that could be stored in a user's computer registry and checked when using a proprietary reader. DRM certificates are most useful and not dependent on an Internet connection, but even though they may use extremely secure encryptions, being stored on the user's computer they can still be exploited and shared. A more secure method was developed for VeryPDF Cloud PDF DRM Protector which utilizes an online service to validate each user according to their unique computer signature.
Limit number of prints of PDF document
Some PDF protection software may provide options for allowing or disabling print, and as we have already mentioned above, that restriction may only be hiding the print button, but not preventing print by other methods such as using a command line. But only few of those applications can effectively control the number of prints allowed. Some may effectively control the number of visits to a printer, in which case on any occasion the user can print 1,000 or more copies, but there is only one application that can effectively control how many prints are made.
Limit number of views of PDF document
As with controlling the number prints, with DRM you can also limit the number of times a PDF can be opened per user. For example an author can set a limit of 5 views of a document after which it cannot be accessed. From a teacher's point of view, if they haven't absorbed the information by then, then their time has run out. Or a document can be set for one view only, after which it becomes inaccessible to that user. Again, VeryPDF Cloud PDF DRM Protector may be the only program that can cater for this feature and remain unexploitable.
Prevent copy of PDF document
Most of the methods described on this page are about protecting PDF, but so far have only been concerned with preventing access to the document's contents. But what can be done about protecting the document's contents from copy while on display? Well when considering all of the methods available today for making a copy by save, Printscreen and all of the screen capture software available today the task can seem daunting. There are some applications that do prevent Printscreen but there is only one that prevents all copy and capture. VeryPDF Cloud PDF DRM Protector provides the most secure document protection and was specially designed for integration with VeryPDF Cloud PDF DRM Protector.
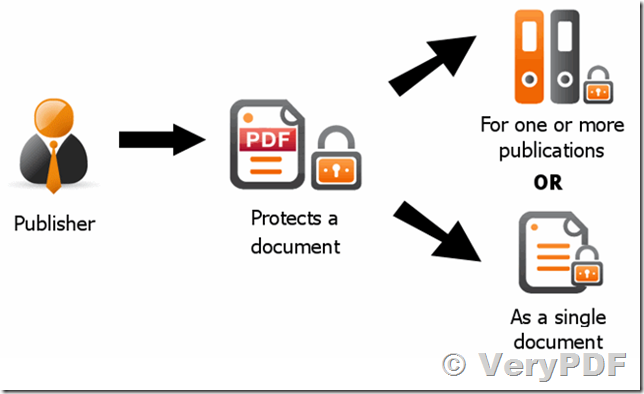
Prevent unauthorized sharing of PDF document
Most people think that because a file can be sent by email that it can been exploited, and in most cases this will be true because nothing will prevent a user from sending any file by email. But there is something that can be done to that file to make it useless to any recipients who are not authorized to read it. For example if DRM is applied to a PDF document then it doesn't make any difference how many users send thousands of copies to any number of recipients, because only those recipients who have the author's permission and the correct reader will be bale to open the document. For more information on how this works with a practical demonstration for evaluation, try creating a demo account with a DRM Service.
* To prevent documents from being opened in generic readers sometimes the file's header is mangled instead of properly encrypting the document. Many programs claiming to use "strong encryption" are actually not encrypted at all.
** There are many programs available today for the extraction of passwords from PDF. Unless the reader and the document are designed from end to end to preserve the integrity of encryption, they can be exploited. Readers such as Adobe Reader are designed to be user-friendly and their source code is available to too many programmers to remain secure.
VeryPDF released a new version of PDF DRM Solution, you may test it from this web page,
http://drm.verypdf.com/online/